TiCon 4 supports Single Sign On with Microsoft Entra ID (formerly Azure Active Directory). To set this up, use the following work steps:
![]() 1. Registration of TiCon as an app in the Azure Directory
1. Registration of TiCon as an app in the Azure Directory
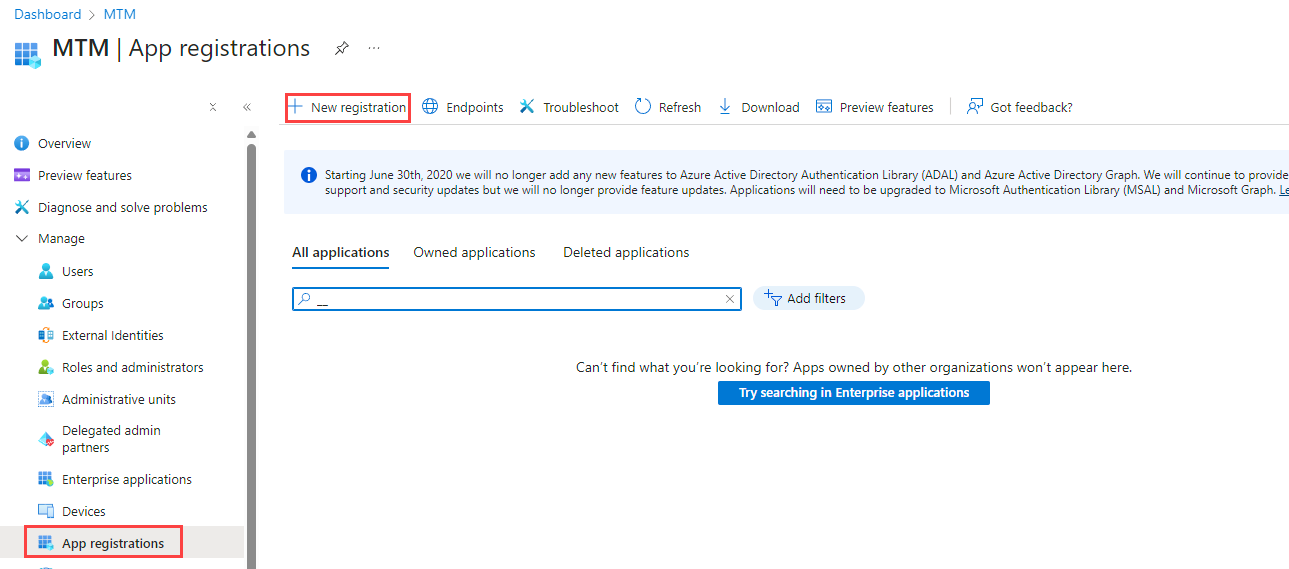
1.1.Access the Azure Portal at https://portal.azure.com and log in. Alternatively, go to "Click", then go to the "App Registrations" area; in this case continue with 1.4. 1.2. Click "Entra ID" 1.3. Click "App Registrations" in the navigation menu on the left side 1.4. Via "+New registration",
1.5.
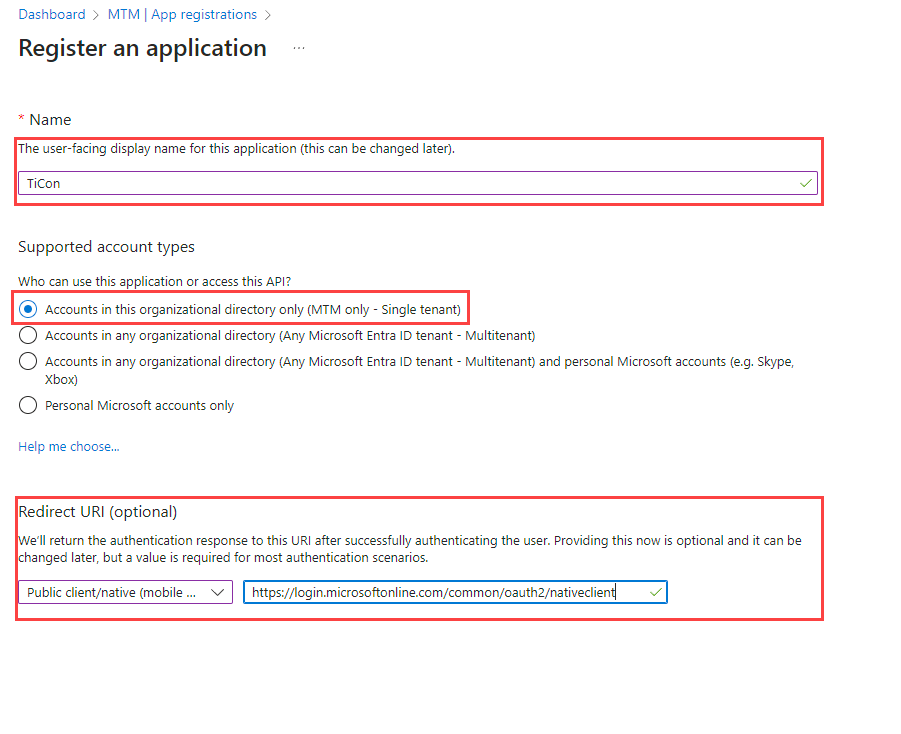
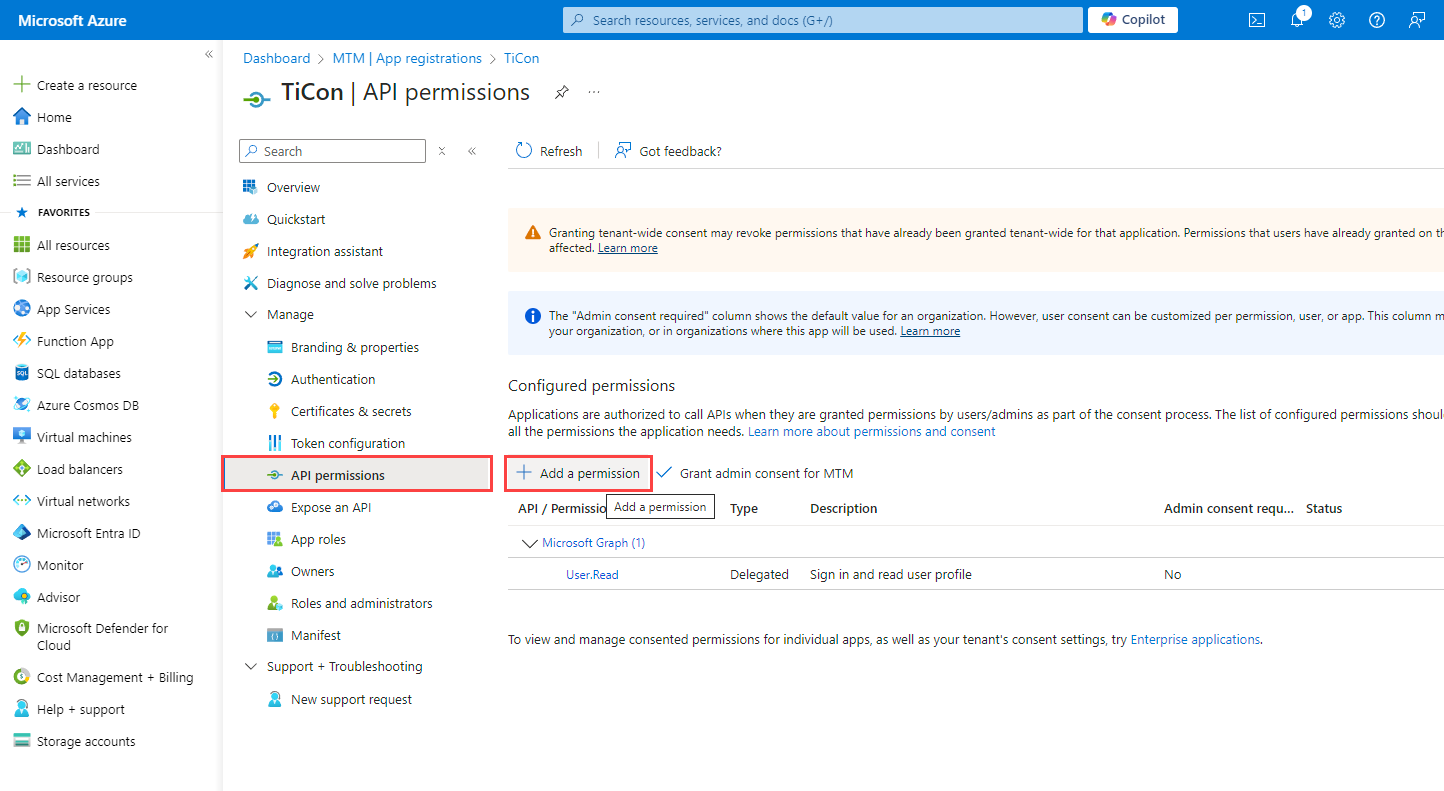
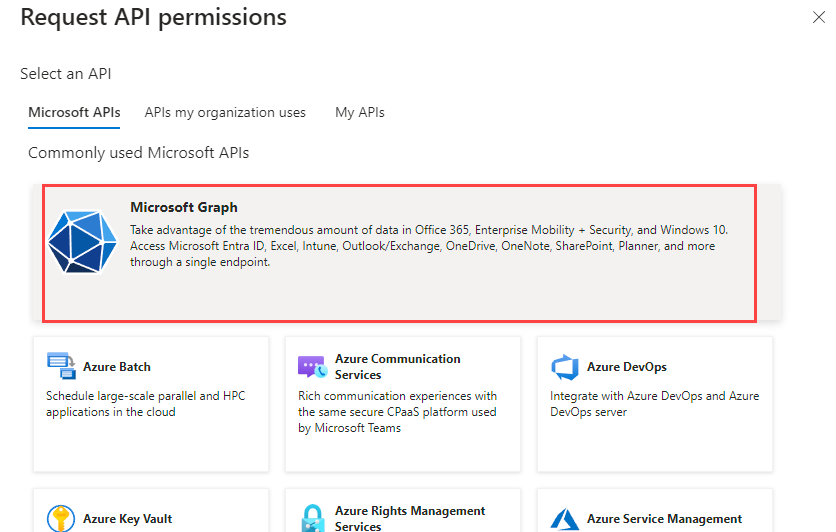
1.6.Single tenantselect 1.7.Under "Redirect URI" (optional), select "Public client/native (mobile & desktop)" 1.8.in the "Authentication" area, add the "Platform configuration Mobile and desktop applications" and enter the Redirect URI "https://login.microsoftonline.com/common/oauth2/nativeclient" 1.9.In the area "App-Registration >TiCon API Permissions" is selected 1.10.by clicking on "+Add a permission" to add a
1.11.In the "
1.12.
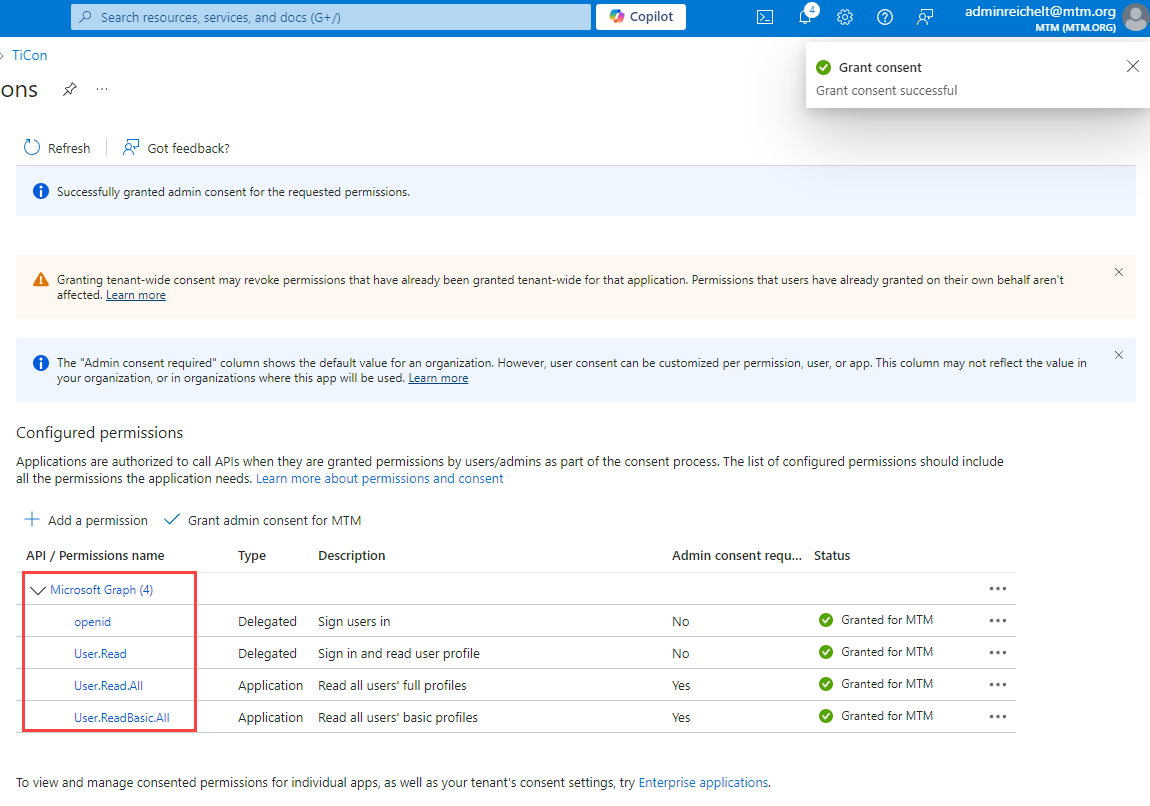
1.12.Grant the following "
▪openid ▪User.Read ▪User.ReadBasic.All ▪User.Read.All ▪Group.Read.All This allows the Entra ID users and groups to be read out with TiCon4. The status must be set to "Granted for...", i.e. an authorized user must still approve these rights. 1.13. Click "Register" to complete the registration 1.14. Then open the new registration, copy the "Application (client) ID" and the "Directory (tenant) ID" as these are required in TiCon4
|
![]() 2. Saving the application (client) ID in the TiCon Administration
2. Saving the application (client) ID in the TiCon Administration
2.1.Start TiCon 2.2.Open TiCon-Admin 2.3.Under "Program" → "General" insert the " Application (client ID) " and "Directory (tenant) ID" (see above) and save 2.4.A dialog for logging into the Azure Portal appears 2.5.There are two ways to log in: 2.6.Use an Azure user who has administrator authorization for app registrations in Azure and grant permission (consent) 2.7.Use an Azure user who does NOT have administrator authorization for app registrations in Azure. In this case, three variants can occur: a.Azure is configured so that the user cannot make a "Request" to the administrator. b.Azure is configured so that the user can make a "Request" for the authorization. c.Permission ("Consent") for the app has already been granted. |
Notes on switching from "Active Directory" to "Microsoft Entra ID"
▪Users created via Microsoft Entra ID can have the same login name as Microsoft Entra ID users, but are considered new users.
▪After creating the Microsoft Entra ID users, the "Transfer user" function can be used to transfer all data of the former Active Directory users to the new Microsoft Entra ID users.
▪Alternatively, after entering the application ID in the database, the SSID of the AD user can be exchanged for the SSID from the Microsoft Entra ID.
▪This means that all users can log in via Microsoft Entra ID and all personal settings and element ownership are retained.
▪The SSIDs can be found in the "ACTAD0E" table.
Troubleshooting
•In some cases, Entra ID needs a few minutes until everything is updated and it is possible to log in to TiCon.
•To test which data is supplied for a user, you can call up the "Query "https://graph.microsoft.com/v1.0/me under "https://developer.microsoft.com/en-us/graph/graph-explorer".
Important: The user must be logged in, otherwise sample data will be displayed.
Note: |
If you have any questions, our support team will be happy to help you at helpdesk@mtm.org or by calling the support hotline at +49 351 26 999 26. |